3D Printing Cybersecurity Gets Boost from DMDII and Others
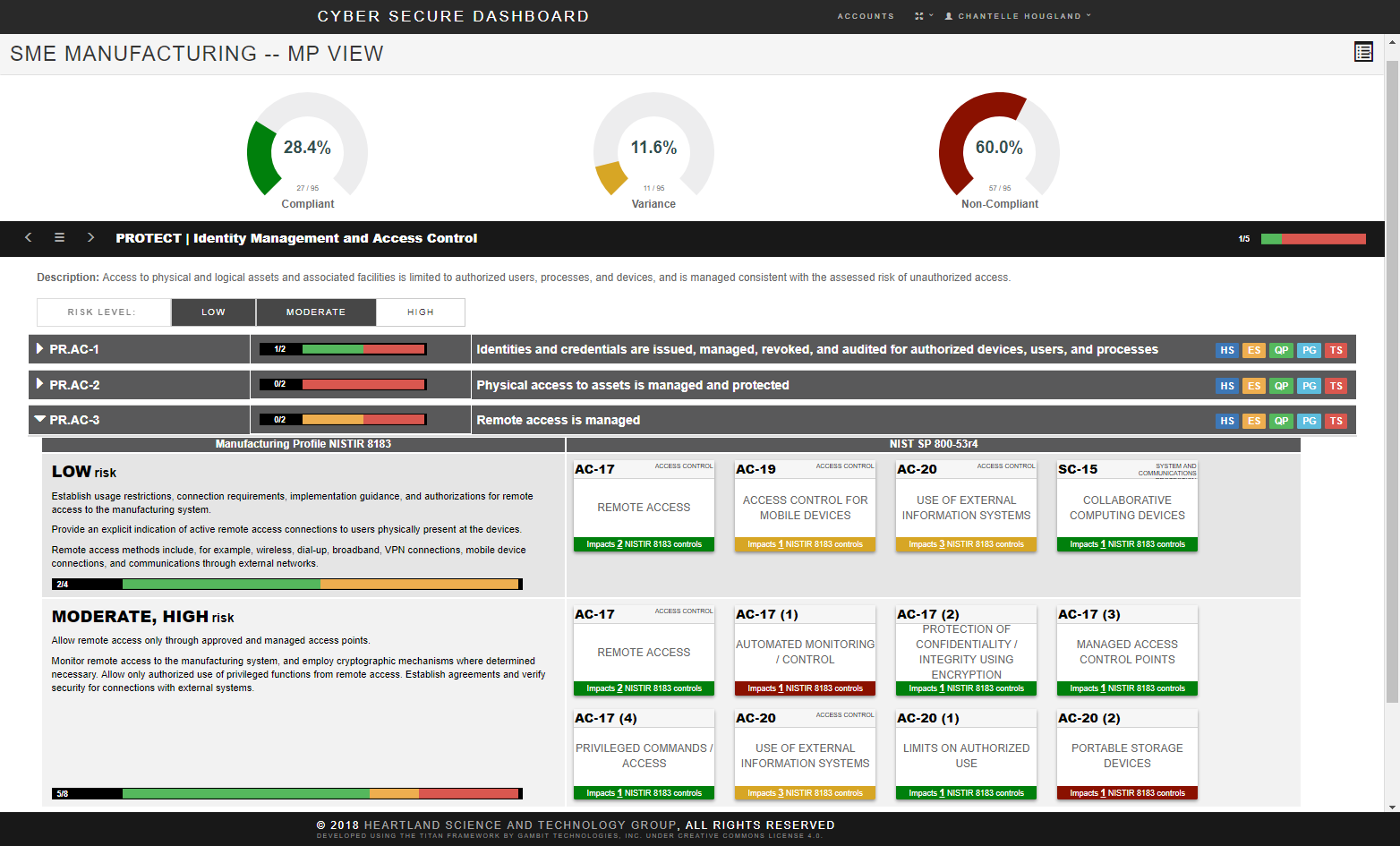
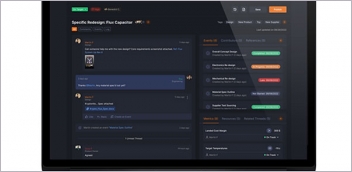
Cybersecurity Dashboard tool: Step by step instructions walk users through the compliance process while providing industry best practices, supplemental guidance, and customizable templates along the way. Here the NIST Manufacturing Profile View (MP View) shows compliance activity and status with active visual cross-referencing to the NIST SP 800-171r1 and NIST SP 800-53r4 controls. The MP View filters requirements based on user-selected risk level (low, moderate, and high). Image courtesy of Heartland Science and Technology Group.
August 21, 2018
As if determining materials, build parameters, support structures and all the other factors for optimized 3D printed production weren’t enough of a challenge — fascinating, but a challenge — the need for keeping data secure is now added to that task list.
For additive manufacturing (AM) a fully digital workflow may incorporate most or all of the following steps and data types: scanned data file, 3D CAD solid model file, STL model file, sliced G-code file, file transfer step, build parameter data (i.e., fill percentage, shell thickness, bed temperature, build speed, laser power, etc. as appropriate), positioning on the build plate, sintering-furnace settings, built-in part identification and more.
How many people across the entire workflow have access to that data? What protections are in place against malware corruption in the file design software code? Are print models protected against loss of intellectual property? Could AM system firmware be hacked at the printer manufacturing plant? Who is responsible for tracking and verifying that each step along the digital path is properly implemented?
 Cybersecurity is becoming a critical element of additive manufacturing. Thirty-five percent of all cyber-espionage attacks in the U.S. are addressed at the manufacturing sector, the largest amount of any single sector, according to the 2017 Verizon Data Breach Investigations Report. Image courtesy of DMDII.
Cybersecurity is becoming a critical element of additive manufacturing. Thirty-five percent of all cyber-espionage attacks in the U.S. are addressed at the manufacturing sector, the largest amount of any single sector, according to the 2017 Verizon Data Breach Investigations Report. Image courtesy of DMDII.These are questions that demand deep answers and form a special cybersecurity challenge for small and medium businesses. Fortunately, universities, consultants and targeted partnerships are addressing different aspects of this new field and sharing the results.
Strength in Numbers, Sharing the Load
To highlight this critical topic, one of the fourteen national Manufacturing USA Institutes created a dedicated cybersecurity task-force. In 2016, Digital Manufacturing and Design Innovation Institute (DMDII) in Chicago, led by the University + Industry (UI) Labs Collaboration group, launched the National Center for Cybersecurity in Manufacturing. Its charter includes a focus on risks to AM and several relevant projects are already underway.
According to the group’s website, “DMDII brings together partners from universities, industry, startups and government to solve technology advancement challenges in digital manufacturing that are too complex for any one organization to solve on its own.” In simpler terms, the Center aims to lower the educational and cost barriers that manufacturing faces to increase readiness for cyber attacks.
Koushik Subramanian, the recently named director of the Cybersecurity Center, notes that the top-level mission at DMDII is, “to make every part better than the last by utilizing digital technologies.” The Center’s role is to create awareness, develop and train the workforce and identify low-cost tools, all focused on security assessments and risk mitigation.
With AM being an inherently digital process, this group’s work is a perfect fit in multiple critical areas. One such project is the Cyber Secure Dashboard, jointly created with the University of Illinois Urbana-Champaign, Lockheed Martin, Heartland Science & Technology Group and others. The initial goal of the project was to develop an assessment tool to help small and medium-sized manufacturers (SMMs) comply with the Department of Defense (DoD) mandated control requirements (NIST SP800-171 r1, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations).
However, Subramanian says, “This project has much broader applicability than just DoD suppliers and is relevant to any manufacturers looking to improve their cybersecurity practices. Today the tool aids manufacturers in developing a cyber risk management process through an easy-to-use, cloud-based software-as-a-service (SaaS) offering. This streamlines compliance and provides manufacturers with industry best practices and policy templates for implementing the cybersecurity controls included in the NIST framework.”
Having started in January 2017, the Dashboard group already released a commercially available solution in early 2018 that includes step-by-step instructions. Interested parties can learn more at cybersecuredashboard.com. A 14-day free trial is available, or an annual licensee can be purchased for $1,500. The Critical Infrastructure Resilience Institute (CIRI) at the University of Illinois at Urbana-Champaign continues to build upon the Dashboard’s core technology.
DMDII completed another AM-related cybersecurity effort in February 2017 in conjunction with one of its member organizations, Imprimis Inc. This project was a case study that assessed the impact of DoD cybersecurity regulation on SMMs as mentioned above. For example, the case study looked at the man hours required to assess cybersecurity practices and the time to complete the mitigations.
Other Commercial Cybersecurity Activities
From using blockchain technology to secure the digital thread of 3D print data (Cubichain Technologies) to employing multiple software protection and validation tools throughout the AM workflow (Identify3D), more companies are turning their attention to AM cybersecurity issues.
Amy Looper, security consultant for Alagen Security Solutions, offers an overview of why this field is exponentially taking off. “Additive Manufacturing (3D Printing) is quickly advancing as global manufacturing and healthcare companies are seeing revenue and the ability to speed innovation through this immersive technology,” she says. “The open source software available in 3D design enables designers to innovate and collaborate, sharing their designs globally; however, that certainly presents risk to intellectual property.”
Looper goes on to say: “This threat exists so much that now the FDA is currently looking at securing medical-device additive manufacturing processes through regulation.”
From a technology manufacturer perspective, says Looper, companies such as Siemens and HP have created coalitions to bring designers, engineers, manufacturing service providers, partners, material providers and software vendors together in one ecosystem. “For example, the goal in Siemen’s Additive Manufacturing Network is to reduce overall risk and improve security by creating some standards,” she says. “(These will) monitor and secure various prototypes and start to serialize production parts within the group for easy reference and tracking.”
There are many factors to consider to improve 3D printing security, Looper notes, from network access control and physical security monitoring of production printers to software development lifecycle security. “All of these are important to reducing the overall threat landscape within the manufacturing and healthcare printing processes,” she says.
Helping the Everyone Explore 3D Printing Cybersecurity
“AM faces many cybersecurity threats including those that are remote, local or physical,” says Subramanian, describing his Center’s work. “Having a non-commercial manufacturing testbed allows DMDII more freedom to explore the benefits and risks of the digital technologies that are transforming manufacturing today. DE readers at small manufacturers and across all sectors should use our findings and research to mature their own security posture.”
For those looking to become involved in a hands-on way, DMDII is holding a Cybersecurity for Manufacturing Workshop on September 25-26 at the UI LABS Innovation Center.
Subscribe to our FREE magazine, FREE email newsletters or both!
About the Author
Pamela Waterman worked as Digital Engineering’s contributing editor for two decades. Contact her via .(JavaScript must be enabled to view this email address).
Follow DERelated Topics