Autonomous vehicle designs are the epitome of engineering designs that incorporates safety and many latest technologies.
Latest News
March 25, 2021
Autonomous vehicle designs are the epitome of engineering designs that incorporate safety and cutting-edge technologies. When all systems and technologies are designed in concert, they provide an autonomous vehicle with astonishing value. Coinciding with the design’s value is the need to protect the autonomous vehicle asset from cyber threats to the vehicle and its systems, as well as threats to the intellectual property of the design that produced it.
To be smart and safe, designers must protect their tangible and intangible assets.
Complex Designs
Autonomous vehicles represent complex designs. Using Lidar and stereo vision, these vehicles’ designs are often coupled with machine learning techniques. With any complex design, after it is completed, others are interested in your secret sauce; how did you come up with the final product? And if history repeats itself, hackers just might want to probe your technology and use it.
Robert Bielby is senior director of automotive system architecture and segment marketing at the Micron Corp. in Folsom, CA. The company provides semiconductor components used in autonomous vehicles. He notes that autonomous vehicles and connected cars offer many features, including in-vehicle infotainment, 4K displays and artificial intelligence-enabled features such as gesture recognition and natural language processing. There’s an exponential increase in memory and compute demands, he notes.
“The challenge with this is building these massive amounts of high-bandwidth, high-performance memory, compute and storage into the small physical footprint of a car,” notes Bielby.
“As an example, if you look at the physical size of a telematics communication unit, it’s a very small space in which you need to cram in the highest possible reliable memory and storage that is essential to store all this code and data,” Bielby adds. “On top of that, it needs to operate in very extreme, high temperatures on the roof of the car in a very thermally challenged environment, which is not optimal for semiconductors. It’s also important that this memory and storage are as low-power and energy-efficient as possible even when processing and storing these huge volumes of data and media; otherwise, drivers will have to constantly be charging their electric vehicles or filling up the tanks of their vehicles—which is costly, inconvenient and detrimental for the environment.”
Protecting Design and Intellectual Property
The autonomous vehicle must not only safely operate, but it must be protected against cybersecurity vulnerabilities. In addition, the precise design parameters of an autonomous vehicle give rise to concerns in safeguarding the intellectual property that created it.
Nicholas K. Terrell is an intellectual property attorney and partner at the Chicago-based law firm of Marshall, Gerstein & Borun LLP. Terrell assists clients in obtaining and protecting intellectual property (IP) rights through development and evaluation of patent portfolios, with a particular focus on electronic systems and software.
“Like any high-growth field, the autonomous vehicles space has seen a land rush in recent years, with inventors staking claims to various aspects of systems, components, manufacturing methods, operational controls and evaluation techniques,” says Terrell. “To be successful, new intellectual property will need to be aligned with solutions to specific issues, which will often be narrower issues arising from implementation of the solutions to more general issues covered by previous patents.”
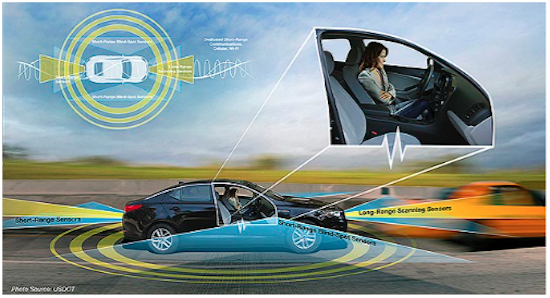
The IP is in a design that orchestrates the complexities of machine vision-based control with software, and sensors, all operating in an environment of fragile connectivity.
“Effective autonomous control through efficient and accurate sensors and robust context-aware machine vision-based control continue to be crucial to the commercialization of autonomous vehicle technology,” adds Terrell. “Beyond the perennial issues of improving vision sensors and software, the competing demands of security and connectivity are among the most significant issues facing today’s autonomous vehicle technology. Vehicle-to-vehicle or vehicle-to-infrastructure communication can improve operational safety, but it can also introduce additional opportunities for malicious attacks and error propagation.”
Protecting Against Cyber Vulnerabilities
Ted Shorter is chief technology officer and co-founder of digital identity security vendor Keyfactor, based in Independence, OH. He emphasizes the importance of cybersecurity and the grave dangers that cyber breaches pose.
He explains that in 2019, a Chinese security firm announced they were able to access the Tesla S driving systems and remotely controlled the brakes in a moving vehicle. Researchers also achieved this with the Jeep in 2015. He says the greatest risks for autonomous cars are navigation, acceleration, braking and steering takeover. In most connected cars, other systems can be targeted such as vehicle locking and remote start systems.
“The threat to autonomous vehicles is real. Like any cybersecurity risk, all consumers with connected devices or online data are at risk,” says Shorter. “But as recent hacks have shown, attacks targeting a make or model’s broad, connected systems could impact an entire fleet of cars simultaneously. The range of impact varies, from inconvenience to potentially life-impacting, depending on the circumstance and point of compromise.”
Shorter adds that any vehicle that connects to or receives a signal from the internet is vulnerable to attack or compromise. If a connected vehicle malfunctions, the impact could be devastating.
Manufacturers are held to a higher standard when it comes to connected car security. They’re improving their product’s security rigor through security best practices like random number generation for connected systems and use of cryptography to securely install firmware and software updates through the lifecycle of the vehicle. He adds that government and industry regulators are putting new guidelines in place to ensure consistency and accountability across the industry.
“Designing new versions of products must focus on security at the start—period,” says Shorter. “Especially if the new generation has more connectivity than the previous one. Security practitioners have learned that getting security ‘right’ must happen at design time; retrofitting and patching can only go so far.”
A New Holistic Mindset
Protecting the design of autonomous vehicles means paying attention to its complexity. Subsequently, it means having a holistic mindset to incorporate and integrate all necessary technologies while being mindful of the threats to intellectual property and cybersecurity.
“This requires a new, holistic mindset in approaching the overall design of the vehicle of the future—one that looks to deploy a robust design with an eye to anticipate updates in the future,” says Bielby. “Long-term success dictates a meaningful shift to a more system-level approach to design to ensure the operation and interaction with all subsystems are well understood and designed upfront with deliberate intent. With both the safety and security considerations associated with addressing this application space, designing the vehicle of the future will attract best-in-class engineers who strive to address some of the greatest engineering challenges of this decade.”
Jim Romeo is a freelance writer based in Chesapeake, VA. Send e-mail about this article to [email protected].
Subscribe to our FREE magazine, FREE email newsletters or both!
Latest News
About the Author
Jim Romeo is a freelance writer based in Chesapeake, VA. Send e-mail about this article to [email protected].
Follow DE