Remedies for Spectre and Meltdown, and their Impact on Engineering Workflows

At Intel’s 2018 CES booth (Credit: Walden Kirsch/Intel Corporation). While participating in the annual tech conference in Vegas, Intel also had to field questions about the recently discovered security vulnerabilities that affect many modern CPUs, including Intel processors.
Latest News
January 17, 2018
The year 2018 started off with quite a shakeup — the discovery of major security vulnerabilities that have existed in the CPUs made in the last 20 years. The twin problems, dubbed Spectre and Meltdown, “affect many modern processors, including certain processors by Intel, AMD and ARM,” according to the researchers at Google Project Zero who went public with the news.
Four days into the new year, the world’s biggest chipmaker, Intel, announced it is “rapidly issuing updates for all types of Intel-based computer systems — including personal computers and servers — that render those systems immune from both exploits (referred to as “Spectre” and “Meltdown”) reported by Google Project Zero. Intel and its partners have made significant progress in deploying updates as both software patches and firmware updates.” The company promises, “By the end of next week, Intel expects to have issued updates for more than 90% of processor products introduced within the past five years.”
This was closely followed by another announcement in which Intel writes, “extensive testing has been conducted to assess any impact to system performance from the recently released security updates. Apple, Amazon, Google, and Microsoft are among those reporting that they are seeing little to no performance impact.”
But the patches are not completely free of side effects, as it turns out. On January 12, The Verge reported “Intel’s Spectre patch is causing reboot problems for older processors.” Intel subsequently acknowledged the issue in “systems running Intel Broadwell and Haswell CPUs for both client and data center. We are working quickly with these customers to understand, diagnose and address this reboot issue.”
Ascertaining how the fixes might impact engineering workflow has been challenging. Many CAD and FEA vendors contacted by DE stated they have not done enough testing with the patches to correctly and fairly assess the impact. If they have, few are ready or willing to publicly discuss their findings.
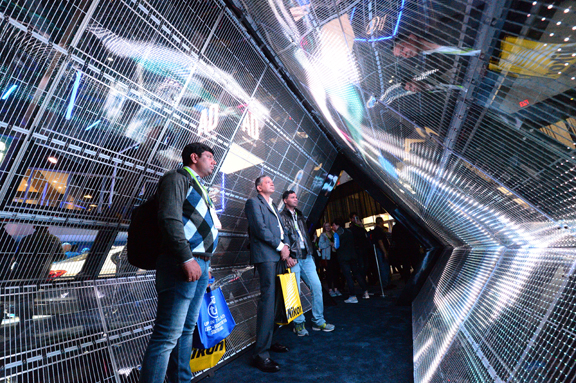 At Intel’s 2018 CES booth (Credit: Walden Kirsch/Intel Corporation). While participating in the annual tech conference in Vegas, Intel also had to field questions about the recently discovered security vulnerabilities that affect many modern CPUs, including Intel processors.
At Intel’s 2018 CES booth (Credit: Walden Kirsch/Intel Corporation). While participating in the annual tech conference in Vegas, Intel also had to field questions about the recently discovered security vulnerabilities that affect many modern CPUs, including Intel processors.Spectre, Meltdown, and CAD in the Virtual Environment
Design software vendor Autodesk’s press office says Autodesk is “actively monitoring the Meltdown and Spectre vulnerabilities and taking steps to protect our customers. We are running benchmarks to determine potential performance impact knowing our customers will be concerned with the performance aspect of the vulnerabilities. We will continue to monitor the issue and provide updates as appropriate.”
Shoaib Mohammad, VP or marketing and business development for workstation maker BOXX, said, “It’s too early to say anything as the workarounds and patches are still being developed and tested.”
“Since most modern CAD workstations are dedicated to a single user doing CAD and would generally have excess CPU resources, most likely the greatest impact will come from reads from storage, especially if the storage is shared across multiple systems (SAN/NAS),” said Jim D’Arezzo, CEO of the Los Angeles-based Condusiv Technologies. “Also, if the CAD systems are virtualized, that too could present significant additional impact due to the HyperVisor containing the actual CPU and having to share the CPU across multiple users.”
CAD users have historically worked on workstations, with generous system memory, graphics and processing power to accommodate the demands of standard 3D design software, such as AutoCAD, Autodesk Inventor, and SolidWorks. However, in the recent years, some companies have also adopted VDI (virtual desktop infrastructure) or cloud-hosted virtual machines for CAD-centric workloads.
D’Arezzo once worked as VP of marketing for Autodesk. His current firm, Condusiv Technologies, specializes in I/O reduction software. Applications that interact significantly with storage benefit from Condusiv’s offerings.
Impact on HPC Workload
Engineering firms that rely on simulation software often deploy high performance computing (HPC), especially in projects where they need to simulate hundreds or thousands of design variants simultaneously to determine the best option. HPC vendors like Rescale have offerings specifically tailored to simulation-driven engineering enterprises.
“HPC will take a substantial hit, especially if there are shared workloads,” according to D’Arezzo. “And if the reason for clusters is to have different segments of a workload run on different systems passing each piece on to the next system, they will experience significant impact due to the need to synchronize the handoffs.”
HPC performance depends on a combination of factors, including CPU speed, I/O speed (which dictates how fast the computing nodes communicate with one another), and network speed. The security patches’ impact, if any, will likely be seen both in on-premise and cloud-hosted HPC clusters.
It’s also unclear how the patches will affect workload and cluster management software, which governs how the computing jobs are distributed and prioritized in the HPC queue.
Intel’s Own Test Results with Security Fixes
On January 11, Navin Shenoy, Intel’s Executive VP and GM of the Data Center Group, published a blog post detailing the company’s own findings on the security fixes’ performance impact.
While maintaining the impact is not significant for average computers, he revealed, “Across a variety of workloads, including office productivity and media creation as represented in the SYSMark2014SE benchmark, the expected impact is less than 6%. In certain cases, some users may see a more noticeable impact. For instance, users who use web applications that involve complex JavaScript operations may see a somewhat higher impact (up to 10% based on our initial measurements). Workloads that are graphics-intensive like gaming or compute-intensive like financial analysis see minimal impact.”
The data is based on testings on several 6th, 7th and 8th Generation Intel Core processor platforms using Windows 10, according to Intel’s blog post.
CAD and simulation users run their software on a mix of systems powered by both Intel Core and Intel Xeon processors. Intel Core is the CPU in some beginners’ CAD workstations, mini- or tiny workstations, and professional mobile tablets. Intel Xeon is the standard CPU for mid-range and higher end workstations used by heavy CAD and simulation software users.
Intel has not yet published any impact results with testing done on Xeon processors.
Subscribe to our FREE magazine, FREE email newsletters or both!
Latest News
About the Author
Kenneth Wong is Digital Engineering’s resident blogger and senior editor. Email him at [email protected] or share your thoughts on this article at digitaleng.news/facebook.
Follow DE