
Sponsored Content
Optimizing Security — Safeguard Your Printing Environment
July 18, 2017
Your large-format printing environment could be vulnerable to data breaches. Here's how you can address common security risks.
Designing Over-the-Air, Secure Devices
July 1, 2017
The fundamentals of IoT device security are hard to build in late in the development process, and the details do matter.
By the Numbers: The Internet of Things
June 2, 2017
Facts and figures on the Internet of Things (IoT).
Sponsored Content
Born this Way: Higher Security for High Speed Computing
May 24, 2017
IDC predicts that, by 2019, 70% of major multinational corporations with roots in the U.S. and Europe will face significant cybersecurity attacks

Sponsored Content
Develop a New HPC Cybersecurity Mindset
May 24, 2017
High-performance computing (HPC) has opened the door to many innovations; yet, it has also introduced new cybersecurity challenges, as the computational power has attracted cybercriminals, as well as malicious insiders.
Balance Cybersecurity & Collaboration
May 24, 2017
Open collaboration raises fears that the system security will be compromised, yet locking a system down hampers research and ultimately interferes with the reasons for providing computing resources.
Cybersecurity, HPC and Big Data
May 24, 2017
In the past two years, IDC’s HPC team (now called Hyperion Research) has conducted major studies on cybersecurity practices in the U.S. private sector, with special attention to the roles of HPC and big data analytics.
Sponsored Content
How IoT Is Making Security Imperative for All Embedded Software
October 11, 2016
Devices for the Internet of Things require secure embedded software. Here's what you can do to improve your code's security while reducing costs and cycle times.
Industrial Internet Consortium Releases Security Framework
September 19, 2016
The framework provides a systematic view at IIoT security.
IoT Security: Smart Measures for Smart Devices
August 1, 2016
Early integration and testing is key for safer products.
Security Frameworks to Set the IoT and IIoT in Motion
June 1, 2016
The IoT market already offers a number of solutions to prevent attacks.
Software Piracy: A Growing Epidemic
May 13, 2016
The practice exposes customers to a range of IT risks.

CeBIT Keynoter Focuses on Securing the ‘Things’ in IoT
March 21, 2016
Lessons learned from hacking the Tesla Model S are applied.

Nissan LEAF Security Flaws Exposed via Hacking
February 25, 2016
The NissanConnect EV app could be hacked via a Web interface to control individual car functions and access journey data.
Owl Computing Named Specialist ICS Security Tool Provider
September 14, 2015
The firm offers cybersecurity for industrial control systems and critical infrastructure.
Latest News

FREE WEBINAR May 27: Addressing the Skilled Worker Shortage with Customized eLearning
In this webinar, you can find out how eLearning and learning management software can help companies fill the skilled trades...
America Makes’ Spring 2024 TRX Explores AM Advancements
The event was a knowledge hub for industry leaders to network and share innovative approaches across design, material, process and...
ELEMENTS Version 4.2.0 Now Released
ELEMENTS 4.2.0 is an open-source computational fluid dynamics (CFD) software suite.
AMEXCI and Nikon SLM Solutions Collaborate in the Nordics
This collaboration is intended to enhance large-scale serial production through additive manufacturing machines, the companies report.
BMF Gets FDA OK for Ultra Thin Dental Veneer Material
Zirconia materials now qualified for use in the production of thin cosmetic veneers, company reports.

Nexa3D and KVG Scale Defense Manufacturing Capabilities
The government contractor adds 15 high-speed extrusion printers from Nexa3D to meet demand for deployable 3D printing, organizations report.
All posts
New & Noteworthy
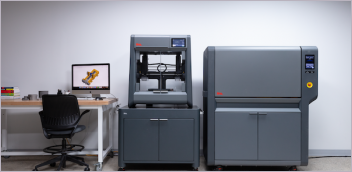
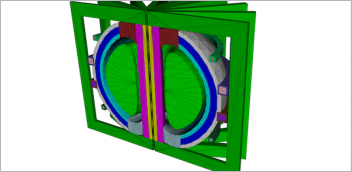
New & Noteworthy: Safe, Cost-Effective Metal 3D Printing - Anywhere
Desktop Metal’s Studio System offers turnkey metal printing for prototypes and...
New & Noteworthy: Direct Neutronics Analysis on CAD
Coreform Cubit 2023.11 workflows enable neutronics directly on CAD for next-generation nuclear energy...
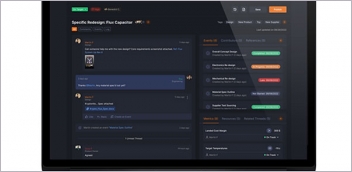
New & Noteworthy: Agile Engineering Collaboration
Authentise Threads is a new software tool for distributed communications and project...

New & Noteworthy Product Introduction: Enterprise VR Headset
Lenovo ThinkReality VRX has an immersive display works with virtual, augmented and...
