Latest News
April 1, 2021
It has now been more than a year since most engineering firms moved to dispersed, work-from-home (WFH) operations. A shift to digital design collaboration had already started, but the COVID-19 pandemic accelerated those efforts. Now, engineering departments realize security measures put into place before WFH continues to evolve.
DE discussed the current state of security in product development with software vendors, computer workstation manufacturers and specialized engineering services vendors. Our conversations centered on how each of them help engineering teams protect their designs, data and intellectual property.
While each had their own angle on what constitutes good security practices for WFH setups, there were some common threads. First, security must be comprehensive. More than one expert referred to it as the onion approach, using many layers of overlapping security. Second, a weakness in any aspect of the system affects the whole system. Third, practices are as important as the technology.
Where is the Workstation?
“At the beginning of the pandemic we thought people would just take their workstations home,” says Rod Mach, CEO and founder of TotalCAE, a provider of cloud-based simulation and analysis services. “They took them home and realized it didn’t work.”
Most engineers were still connecting to either a workstation or a server at the home office.
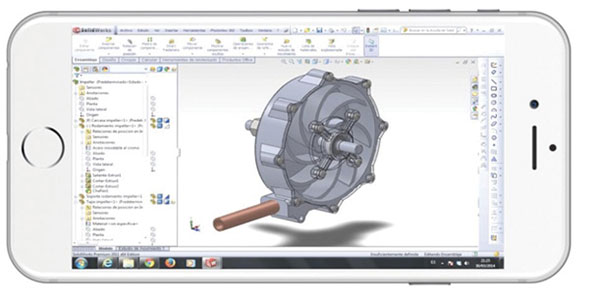
Mach says many of his clients are now using remote visualization, a technology that performs the engineering on a cloud server or a high-performance computing (HPC) cluster, then transmits only the images to the end user. The user can run the CAD or CAE program as if it were running on their local computer, but only pixels are being transmitted back and forth between the remote user and the centralized server or cluster.

“The technology already existed,” Mach notes. “Now there is much more interest.”
Having engineering models on a device outside the office—and its firewall—is a scary notion for IT departments, Mach says.
“Having an encrypted laptop at home does not prevent someone from accessing your home network,” Mach adds.
One TotalCAE customer is a large automobile manufacturer that started using remote visualization before the pandemic.
“Now they like it because remote users don’t download data,” Mach notes. “You can’t ‘thumb drive’ a model from the visualization. Securing data from theft is easier.”
Mach says TotalCAE customers seem to be gravitating toward three remote visualization services: FastX from StarNet Communications; ZCentral Remote Boost from HP; and NICE DCV from NI SP GmbH, which is offered by Amazon Web Services (AWS).
“While these solutions are not new, because of the pandemic we have seen a large uptick in their usage,” Mach says. “They all have provided additional security benefits to clients. These solutions will likely persist even after things return to normal, as clients realize the benefit of having a solution for secure remote access to engineering data.”
CAD as a Service
“Security is not just about technology, it is also about practices,” says Jon Hirschtick, general manager of Onshape and Atlas at PTC. “Most hacking is social engineering,” and security has to be built in. “Work from home is ‘work from what device?’ Sometimes you can’t guarantee how a remote user is connecting to the company server,” he adds.
In the “old days” of standalone CAD workstations using servers to share files, Hirschtick says it was “CAD first, then data management, then security.” Engineering needs to reverse that order, making security first, then data management and finally the CAD program.
Hirschtick speaks from his experience in bringing Onshape to market. Onshape remains the only purely cloud-based product development CAD product. When PTC acquired Onshape in 2019, Hirschtick became a PTC senior vice president and oversaw the company’s Software-as-a-Service division. Using Onshape, the data is stored in one place, on the cloud server. Files are never copied, even if several people share design access.
“We don’t put a copy of data on anybody’s computer. It doesn’t exist there; it can’t be stolen,” Hirschtick says.
Access rights can be set so a user can edit data but not download a copy, and there is a complete audit trail of data use. There is no software to install; Onshape works from any up-to-date web browser.
Hirschtick says that while he promotes the Onshape paradigm as the new order of things, he still realizes that not everyone can stop using their existing software and jump into CAD as a service. He recommends “complete virtualization,” where the application is hosted at the home office and remote users access it using a virtual private network (VPN).
“Complete virtualization is reasonably secure,” Hirschtick says. “It’s the best you can do with the copy/paste paradigm.”
Virtualization is also known as virtual desktop infrastructure (VDI). One powerful workstation or server can host multiple instances of remote access, with each user getting the equivalent of a desktop experience. Some companies use VDI to keep intellectual property on-premises. Others use it to provide top-of-the-line hardware resources to more users. A workstation equipped with two or more high-end graphics processing units (GPUs) can provide a pool of users access to the same hardware for much less than equipping each user with an equivalent physical workstation.
Virtualization software is available from several vendors. Commonly used engineering offerings include Rescale; Nutanix Frame (formerly Frame from Mainframe2); Teradici Cloud Access Software; VMware; VirtualBox (open source, supported by Oracle); QEMU KVM (open source, Linux only); Citrix Hypervisor (open source, supported by Citrix); Xen Project (open source, supported by The Linux Foundation); Dell Custom Virtual Desktop Interface, based on Teradici technology; and Mechdyne TGX.
Securing Email for Data Exchange
“Email is a big gaping hole for security,” says Brian Schouten, director of technical presales at PROSTEP. “The easiest way to communicate is what many will use.”
PROSTEP offers OpenDMX GlobalX, software for managed file transfer (MFT). Engineering clients use it to transfer various data and document types between customers, suppliers and partners.
PROSTEP was started as a German consortium of automotive manufacturers. Its first initiative was the STEP file format, an ISO standard still in common use today. OpenDMX GlobalX works with email protocols to create a secure file transfer system on the desktop. The software integrates well with digital twin/digital thread workflows, Schouten says.
“The master copy is stored the right way, not through an active process but through a backend process of systems integration,” Schouten says.
OpenDMX Global X can be on-premise or cloud-based. Schouten recommends Microsoft Azure Government and AWS as good cloud services for hosting an OpenDMX GlobalX installation.
“They have good practices for security,” Schouten explains. “But remember the onion approach. They have their own onion, and you have yours.”
“Security and collaboration are sometimes at odds with each other,” Schouten says. “The more secure the environment, the less you can share data. Practices for making this easy and transparent is an IT issue.”
Schouten says one PROSTEP customer is a defense specialist that is “always pushing up against” security considerations. Sometimes the problems are as low level as what computers they can use on the secure networks. More common is establishing separate networks to isolate usage by data type or user requirements.
“To get to the network, to get to the web, should be like layers of an onion,” he says.
Security by Design
Autodesk has generally taken a hybrid approach to cloud technology usage. Most of its software products are desktop applications extended into an ecosystem using cloud services.
Autodesk does not differentiate between working from home or working from the office, says Reeny Sondhi, chief security officer.
“We aim to make customers’ files equally secure when they’re in our care, regardless of whether a file is worked on from inside the firewall at the office, on a workstation at home or on a laptop in a café.”
Sondhi notes that a crucial factor that affects data security is that data must be encrypted both when it’s stored “at rest” and when it’s “in transit” to the engineer doing the work.
“Autodesk takes a holistic approach to security and believes it should be built into the system at every level and throughout the process,” Sondhi says. “This is what we refer to as security by design.”
“We find bolt-on security doesn’t scale nor protect data effectively,” Sondhi says. “Security needs to be integrated into the applications, the platform and the infrastructure on which these applications run.”
Regarding the use of cloud software in engineering, Sondhi explains that “the greatest difference in data security when using cloud software is that the cloud helps ensure best-in-class security is both affordable and hassle-free for the customer.”
“Of course, just like any security measure,” Sondhi says, “if you use even the best lock in the world but you leave the key under the mat, your house won’t be very secure. It’s more important than ever today that customers work in partnership with cloud software providers, consistently follow security best practices such as choosing complex and unique passwords, protecting identities and log-in credentials, and utilize valuable security features such as two-factor authentication.”
Optimize for Speed
Key to WFH infrastructure is faster network technology, says Nick Pandher, product manager at BOXX Technologies.
“What made the transition to heavy remote GPU use is the ability to make the user feel like they are working on a physical workstation. As long as you have the right latency experience, remote users will see a performance uplift,” he says.
BOXX is introducing BOXX Cloud, technology for private, high-performance cloud-hosted workstation access. BOXX Cloud is based on BOXX Flex systems, a rack-mounted blade server system using workstation components.
“Too many [engineering companies] run workstation apps on servers not optimized for engineering work,” Pandher says. “Specific CPU and GPU settings are required.”
BOXX believes a core tenet of remote work for engineering should be “if implemented correctly the remote workstation can be more secure than one in your own building,” says Tim Lawrence, BOXX founder and CTO.
Part of the additional security is the use of “air gaps,” which means there is a server not connected to the internet. Another server for outside access is the only device to directly connect to the data server.
Remote delivery is not the major bottleneck for remote delivery of engineering services, says Pandher; the sharing of CPU and GPU time is the bigger problem. The BOXX method connects one remote user to a dedicated workstation blade, which he says makes the system faster than virtualization for engineering.
“Virtualization does have its place in the stack for economic reasons,” says Lawrence. “But virtualization is contrary to optimal performance for engineering. Where performance drives productivity, VDI is not the best tool.”
Being Sneaky With Intellectual Property
IronCAD is a product development application known for its ability to work with various data sources. In the work-from-home era, IronCAD President Tao Yang Han says multiple authorization levels are important.
The most common level is authorization via password. The next level up is authorization by role, allowing access to specific directories or features. A third level is additional authorization.
“All of these are on the application side,” says Han. A fourth level of protection will be forthcoming soon in IronCAD—encryption. “Even if hacked, the intruder won’t understand the data.”
WFH adoption increases the risk of a data breach, Han notes. He says IronCAD works with customers to help them select a remote collaboration and access system that matches their situation. For some customers, an added sneaky step is to substitute a standard part inside an assembly when sharing with certain suppliers.
“Visualize a substitute but don’t use the secret proprietary piece,” Han says.
More TotalCAE Coverage
Subscribe to our FREE magazine, FREE email newsletters or both!
Latest News
About the Author
Randall S. Newton is principal analyst at Consilia Vektor, covering engineering technology. He has been part of the computer graphics industry in a variety of roles since 1985.
Follow DE